The cybersecurity landscape is constantly evolving, with new threats emerging daily. To combat this, security professionals need robust tools that can keep pace with the sheer volume and sophistication of cyberattacks. This is precisely why the Cybersecurity and Infrastructure Security Agency (CISA) has made a significant stride forward by publicly releasing Thorium, a powerful new platform for forensic analysis and malware investigation.
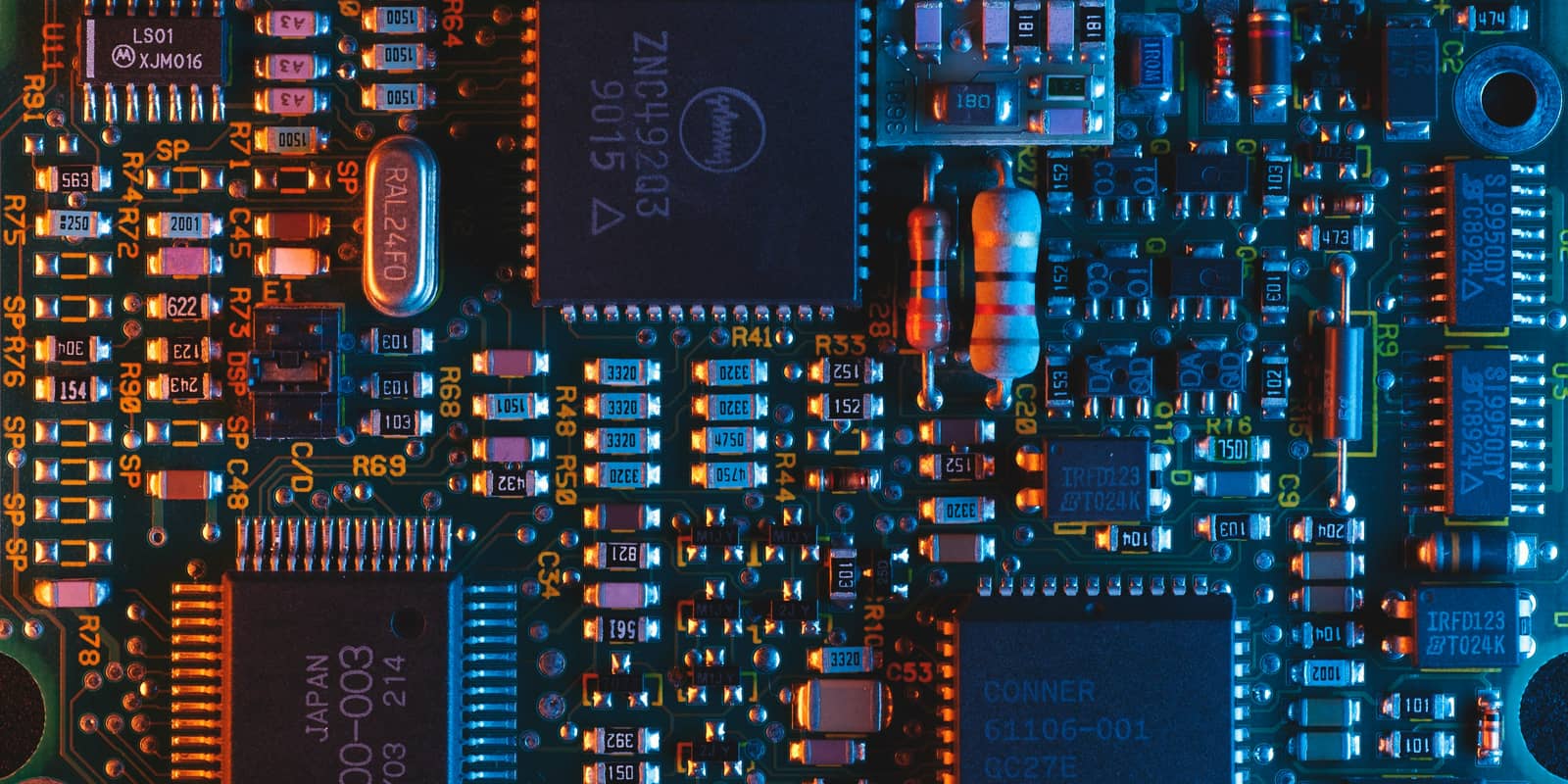
Thorium is designed for cybersecurity specialists in both the public and private sectors, offering unparalleled capabilities for critical functions like cyberattack analysis and incident response. Its impressive performance metrics speak volumes: Thorium can schedule over 1,700 tasks per second and process more than 10 million files per hour per permission group. This remarkable speed and efficiency are crucial for rapidly dissecting complex cyber incidents and understanding the full scope of a breach.
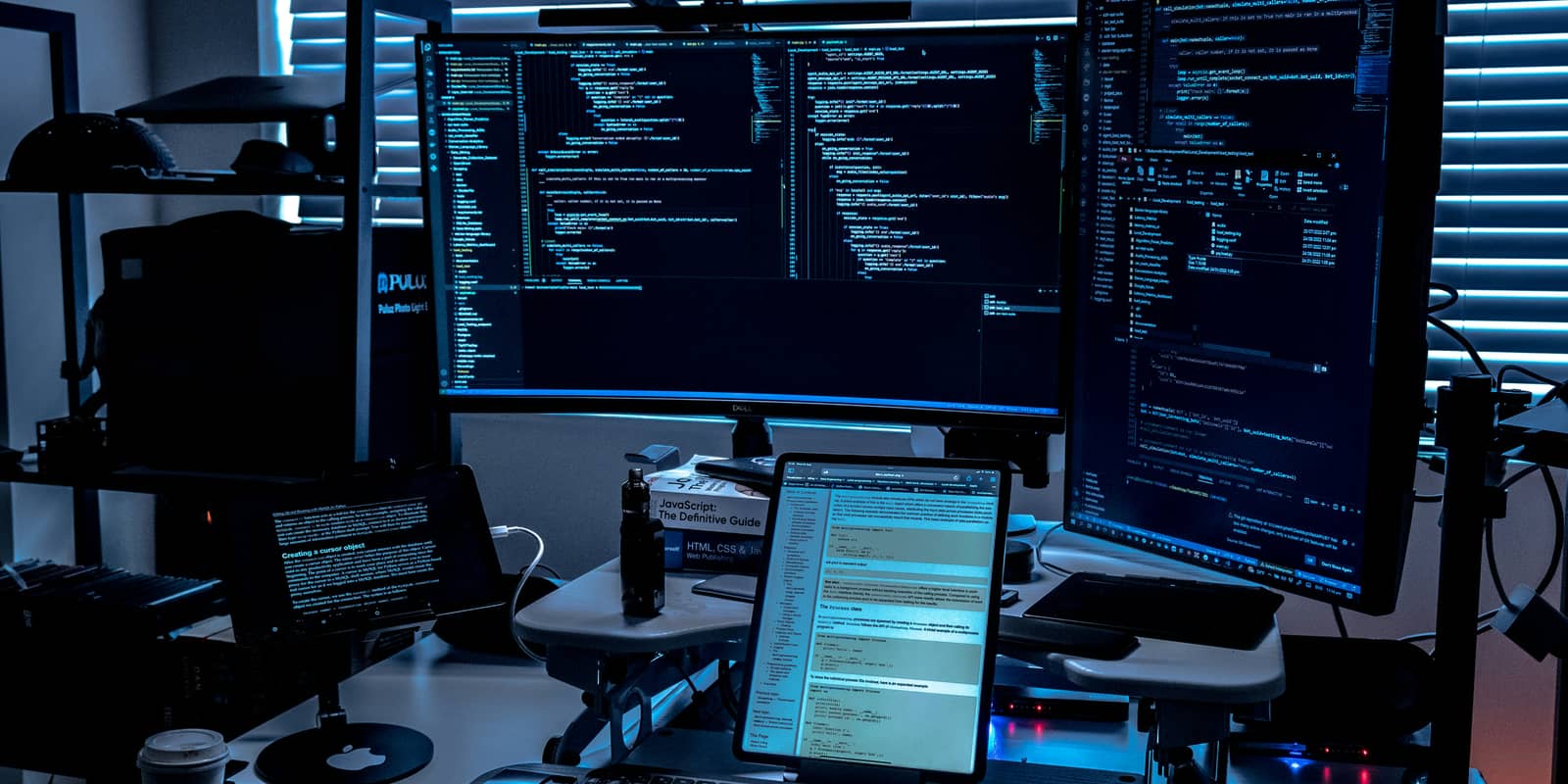
Beyond its raw processing power, Thorium boasts seamless integration with command-line tools, including Docker images. This flexibility allows security analysts to incorporate Thorium into their existing workflows and leverage a wide array of specialized utilities, enhancing their investigative capabilities.
The decision by CISA to make Thorium open-source is a testament to their commitment to fostering a stronger, more collaborative cybersecurity community. The source code is readily available on GitHub in the "cisagov/thorium" repository, enabling transparency, peer review, and community contributions. This open approach encourages innovation and allows security experts worldwide to benefit from and contribute to the platform's development, ultimately strengthening our collective defense against cyber threats.
Thorium represents a significant advancement in the field of digital forensics and malware analysis. Its public release by CISA provides a valuable resource for cybersecurity professionals, empowering them with the tools needed to effectively respond to and mitigate the impact of cyberattacks, safeguarding critical systems and data.