Security
Showing 12 of 81 articles · Page 1 of 7

iPhone Security Flaw Allows Unauthorized Payments via Visa Express Mode
New iPhone flaw allows hackers to bypass locks and steal funds using Visa Express Mode. Learn how this NFC exploit works and what Apple and Visa are saying.
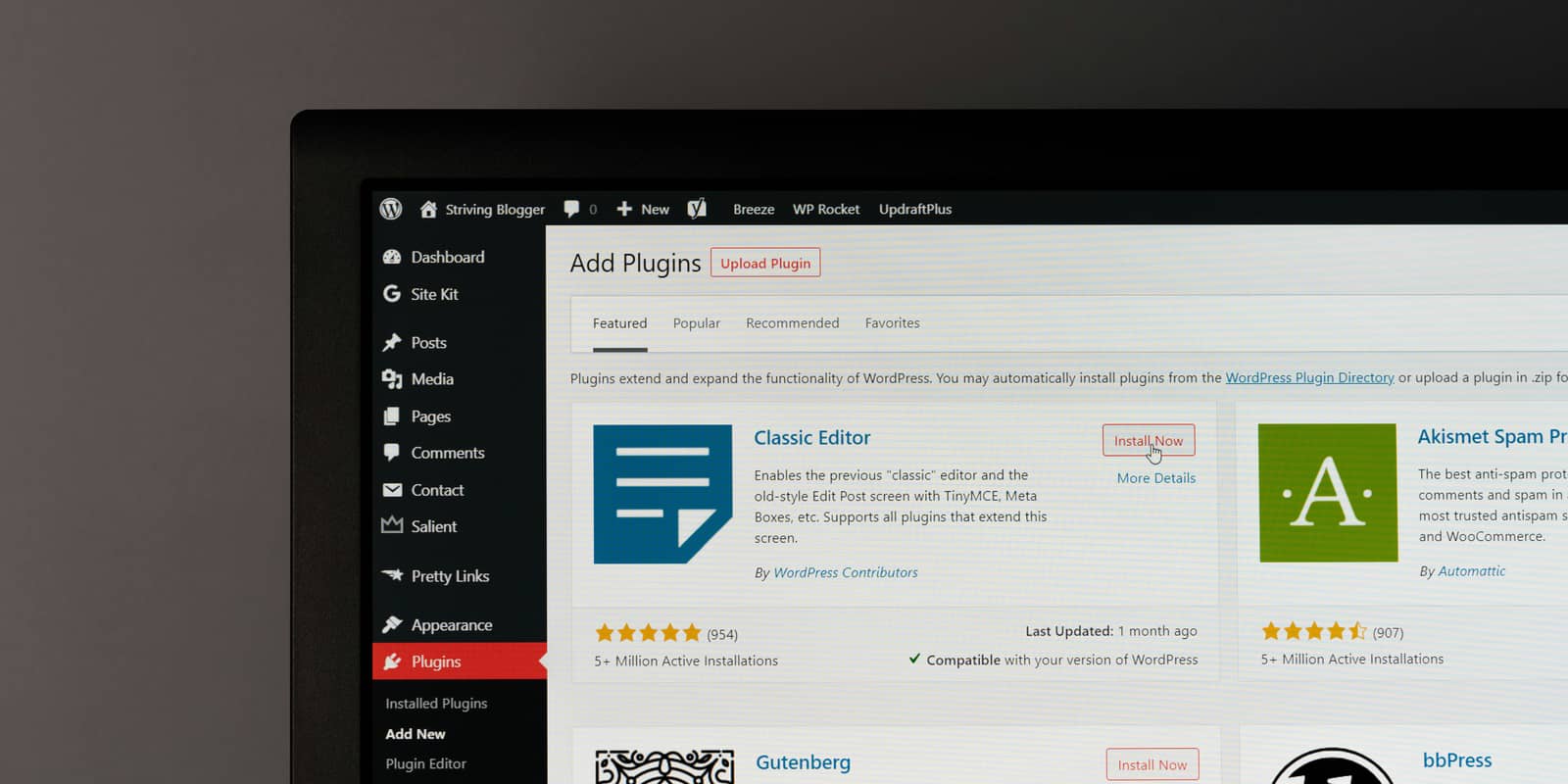
WordPress Security Alert: Popular Plugins Injected with Malware
Over 30 popular WordPress plugins were bought on Flippa and injected with malware. Learn about the backdoor vulnerability and how to protect your website.
Critical Zero-Day Vulnerability Found in Adobe Reader via Malicious PDFs
Hackers are exploiting a critical zero-day flaw in Adobe Reader using malicious PDFs. Learn how to protect your data from this sophisticated cyberattack.
Google Links Axios Library Attack to North Korean Group
Google links Axios library supply chain attack to North Korean group UNC1069. Affected versions: 1.14.1 and 0.30.4. Remove and rotate credentials immediately.

Anthropic's Claude Code Source Code Leaked via NPM
Anthropic's Claude Code source code leaked on NPM due to an accidental source map inclusion. Reconstructed code is now available on GitHub.

Alert: Malicious Code Found in Popular PyPI Package 'telnyx'
Critical security alert: Malicious versions (4.87.1 & 4.87.2) of the telnyx PyPI package found stealing data. Remove immediately and rotate credentials.
BTG Pactual Suspends Pix Operations Following Cyber Attack
BTG Pactual suspends Pix operations after a R$100 million cyber attack. No customer data was compromised. Get the latest details on the security incident.

Meta Internal Security Breach: AI Agent Misstep Exposes Sensitive Data
Meta employees gained unauthorized access to sensitive data after an AI agent error. Learn how an internal forum post triggered this two-hour security breach.

Critical iOS 18 Vulnerability: 'DarkSword' Attack Risks Sensitive Data
New DarkSword attack exploits iOS 18 vulnerability via Safari. Learn how to protect your iPhone data and why you must update to iOS 18.7.6 immediately.

Russian Hackers Target Signal and WhatsApp Users
Russian hackers are targeting Signal and WhatsApp via phishing. Learn how to protect your messages from these sophisticated social engineering attacks.

Chinese Hackers Use Google Sheets to Control Malware Across 42 Countries
Chinese hacking group UNC2814 used Google Sheets to control GRIDTIDE malware in a global espionage campaign targeting 42 countries and telecom data.
Bing AI Recommends Fake GitHub Repositories Distributing Malware
Bing AI is recommending fake OpenClaw GitHub repositories that spread data-stealing malware on Windows and macOS. Learn how to protect your data from this threat.